Step 3. Specify IAM Identity
At the Account step of the wizard, do the following:
- If you have selected the Automatic option at the Configuration Mode step of the wizard, specify one-time access keys that will be used to create the Impersonation and Default Backup Restore IAM roles. For more information on the IAM roles, see Required IAM Permissions.
- If you have selected the Manual option at the Configuration Mode step of the wizard, specify the Default Backup Restore IAM role that will be added to the Veeam Backup for AWS and used to perform operations.
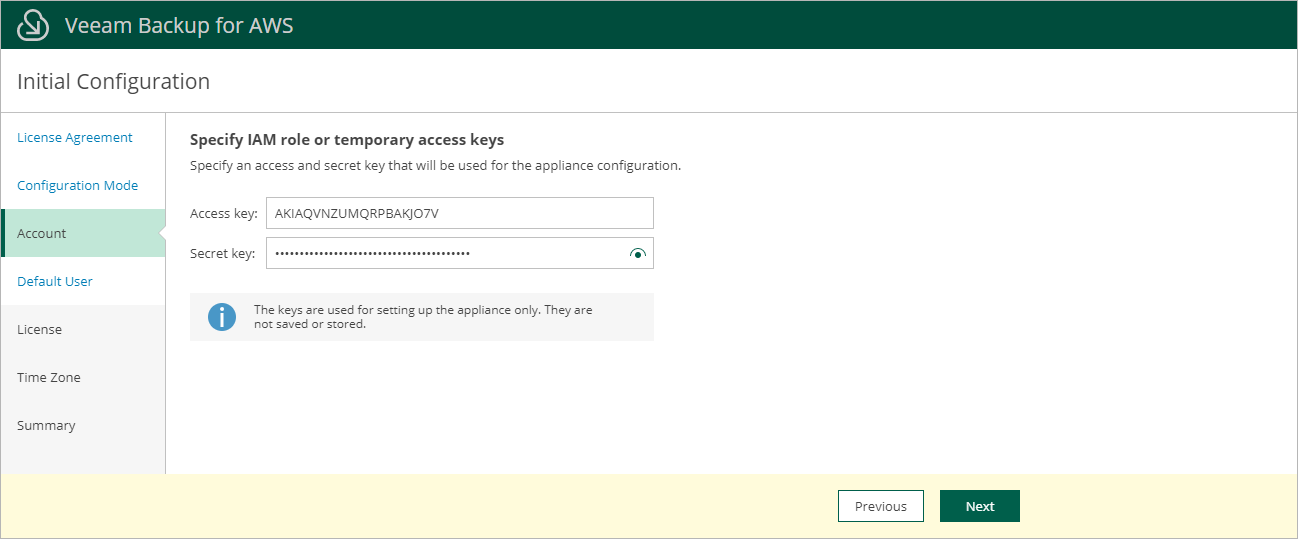
Specifying One-Time Access Keys
To specify the access key ID and the secret access key of an IAM user, use the Access key and Secret key fields. Note that the IAM user must be authorized to create IAM roles. To learn what permissions the IAM user must have to create IAM roles, see Required IAM Permissions.
Note |
Veeam Backup for AWS does not store one-time access keys in the configuration database. |
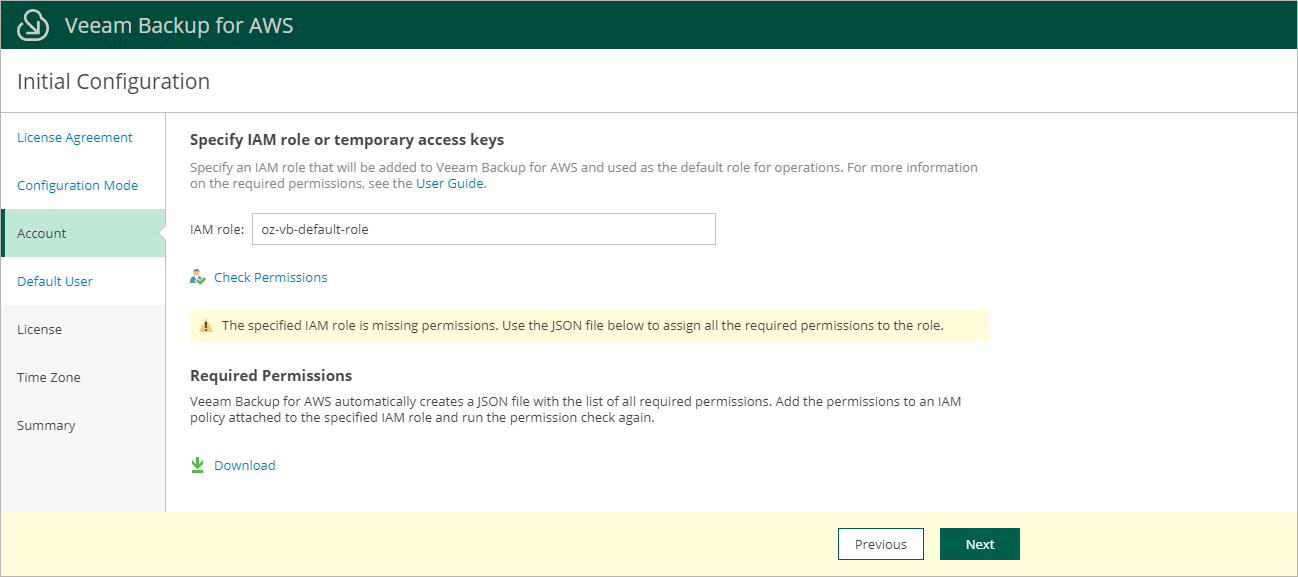
To specify the Default Backup Restore IAM role, enter the IAM role name specified in AWS when creating the role. The IAM role must be created beforehand as described in section Required IAM Permissions.
Note |
If there is a path identifying the IAM role, you must specify the role name in the PATH/NAME format (for example, dept_1/s3_role). To learn how to add identifiers to IAM roles, see AWS Documentation. |
You can check whether the specified IAM role has permissions required to perform all Veeam Backup for AWS operations. To run the IAM role permission check, click Check Permissions. If some permissions of the IAM role are missing, Veeam Backup for AWS will display a warning, but you will still be able to proceed with the wizard without granting the missing permissions to the role. To learn how to grant permissions to IAM roles using the AWS Management Console, see AWS Documentation.
Tip |
You can grant permissions to this IAM role and add other IAM roles that will be used to perform backup and restore operations later, after the backup appliance configuration completes. For more information, see Managing IAM Roles. |