Adding Multi-Geo Microsoft 365 Tenants
To start protecting Microsoft 365 multi-geo tenant data, you must add the Microsoft 365 multi-geo tenant to Veeam Data Cloud.
Consider the following:
- Before you start adding the multi-geo tenant, check Considerations and Limitations.
- Veeam Data Cloud supports multi-geo tenants for Flex backup policies.
To add a Microsoft 365 multi-geo tenant, use the Add Microsoft 365 tenant wizard and do the following:
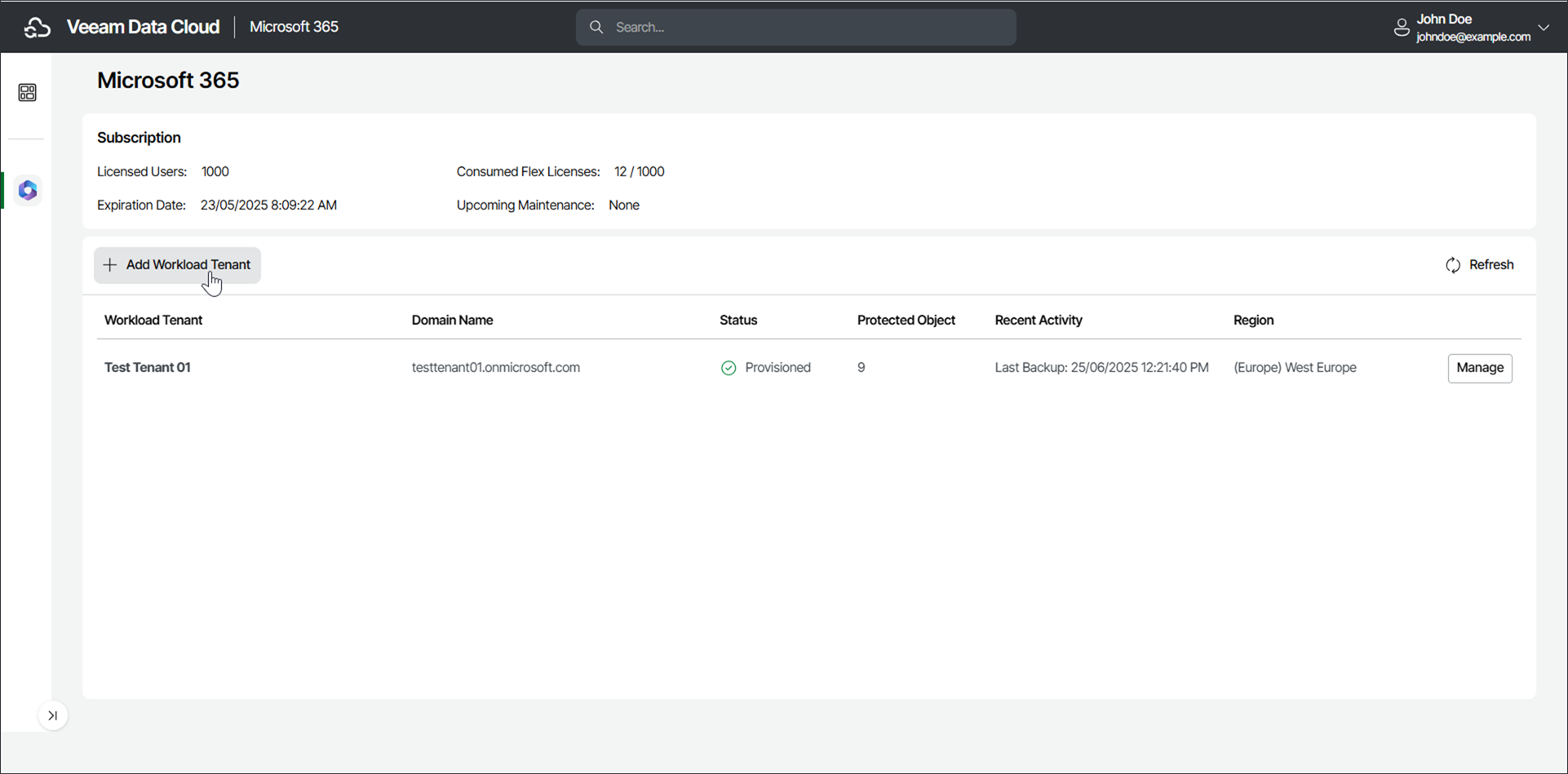
- Click Microsoft 365 on the left to open the list of Microsoft 365 tenants.
- Click Add Tenant.
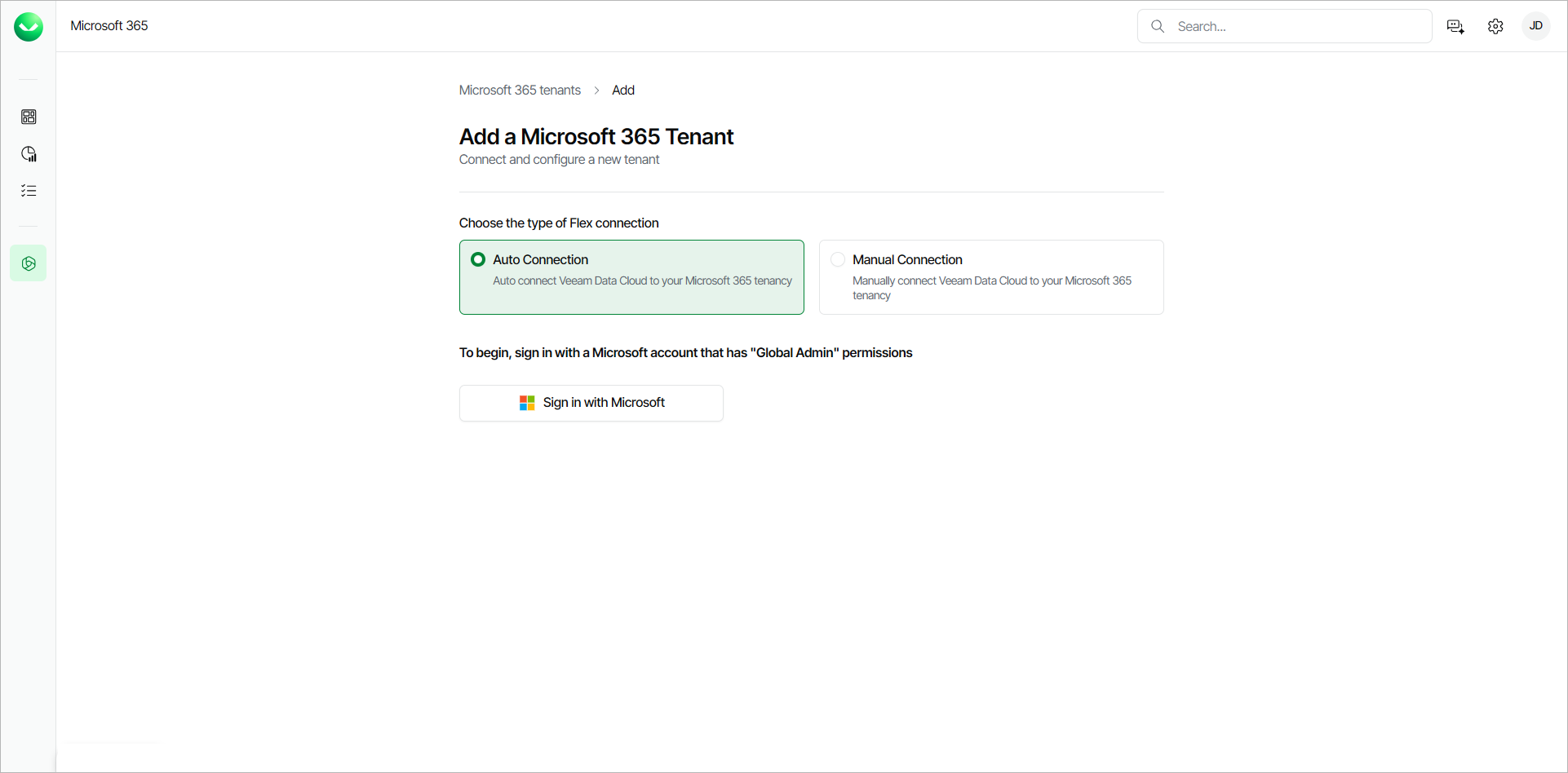
- Choose how you want to connect Veeam Data Cloud to the Microsoft multi-geo tenancy:
- Auto Connection. Select this option if you want to automatically connect Veeam Data Cloud to the Microsoft multi-geo tenancy. This option is recommended and selected by default. Follow the Automatic Connection Steps instructions to proceed.
- Manual Connection. Select this option if you want to manually connect Veeam Data Cloud to the Microsoft multi-geo tenancy. Follow the Manual Connection Steps instructions to proceed.
|
note |
|
To perform the steps successfully, you must use a Microsoft 365 Global Admin account. |
If you choose to automatically connect Veeam Data Cloud to your Microsoft 365 multi-geo tenancy (recommended), do the following:
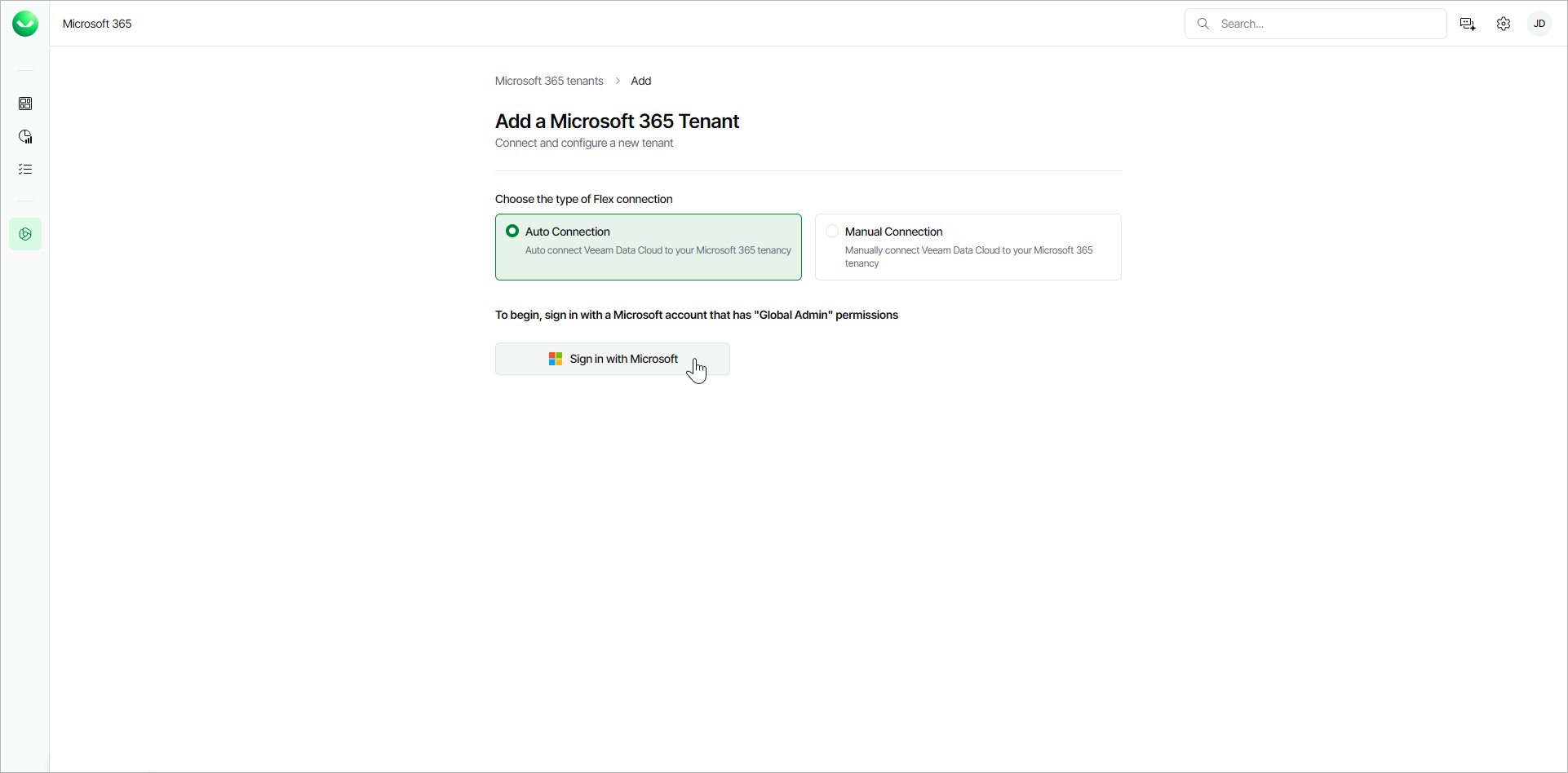
- In the Choose the type of Flex connection section, select Auto Connection.
- Click Sign in with Microsoft.
- In the Microsoft authentication window, select the Microsoft account under which you want to authenticate against Microsoft 365. The account must have the Microsoft 365 Global Admin permissions.
- Accept the required permissions.
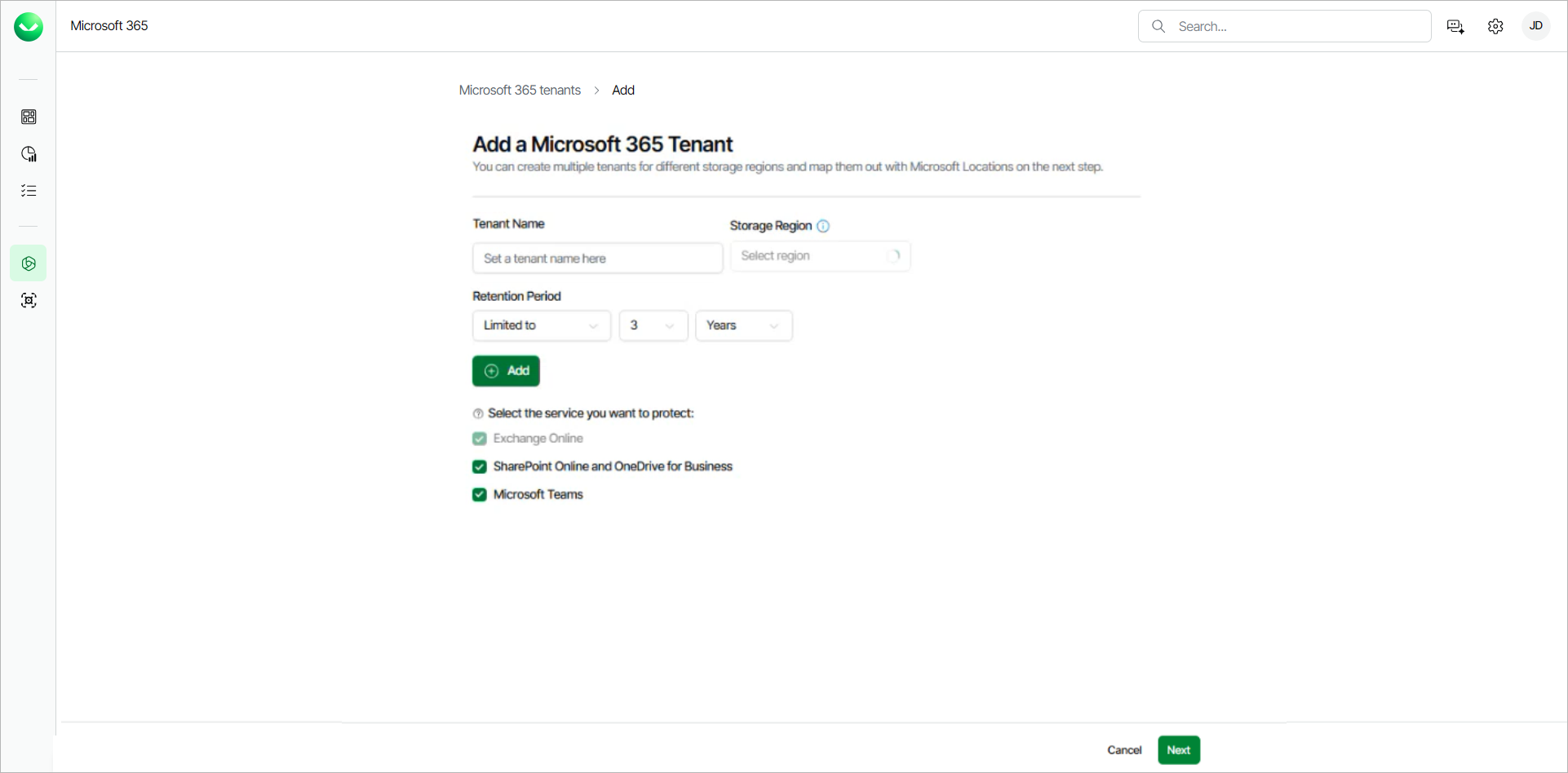
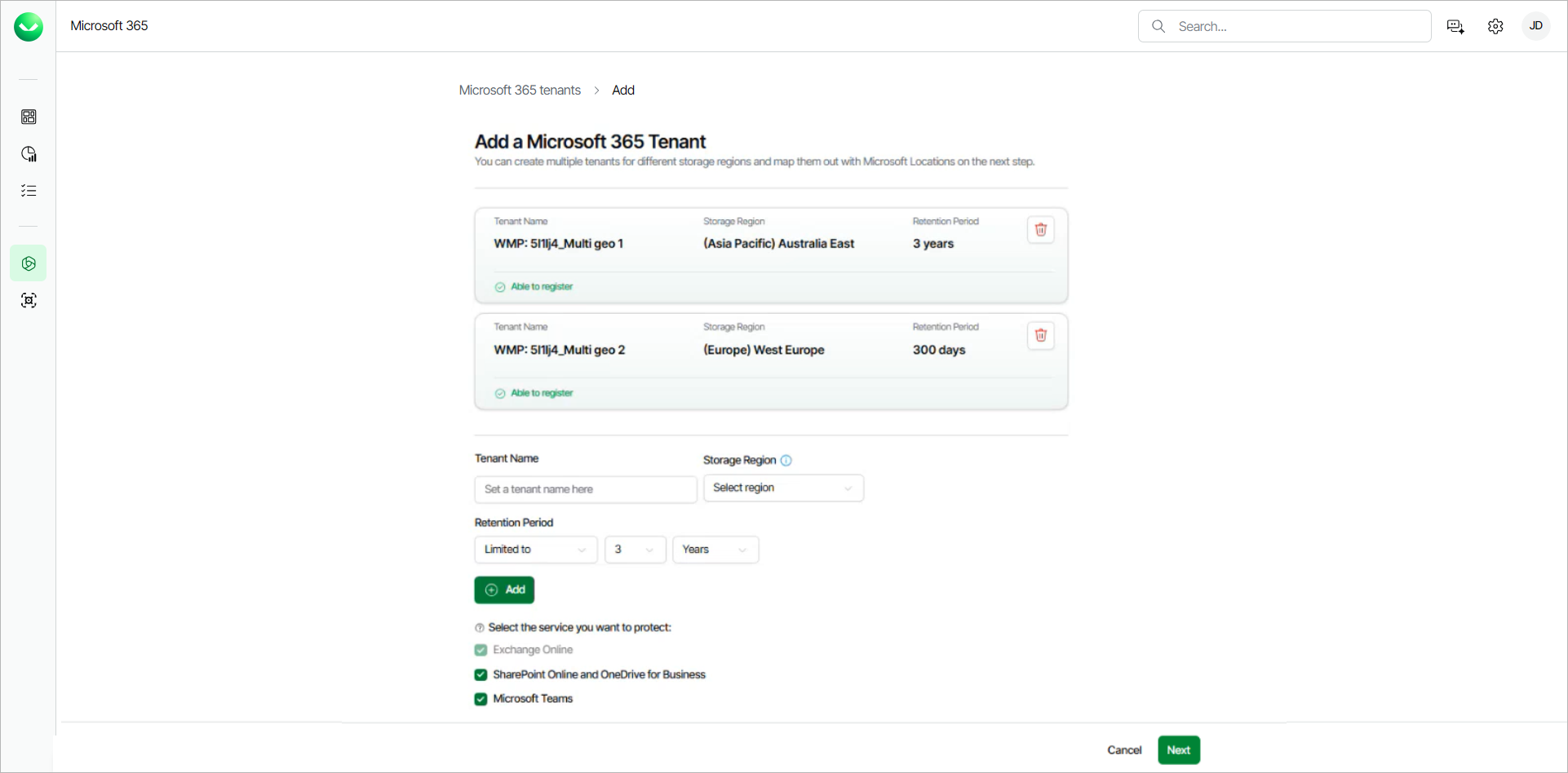
- Return to Veeam Data Cloud and specify the multi-geo tenant settings:
- In the Tenant Name field, specify a name for the new tenant.
- From the Storage Region drop-down list, select a Microsoft Azure region where the backup infrastructure and storage will be provisioned.
For information on supported Microsoft Azure regions, see Backup Storage Regions.
- In the Retention Period section, set the number of Years or Days for the retention period of your backups, or select Unlimited to keep the backups for an indefinite time.
Once you set the retention period, you cannot reduce it. For more information, see Backup Retention.
- In the Select the service you want to protect section, make sure to select only the services that are available in the Microsoft 365 tenant that you are connecting to.
Veeam Data Cloud sets the first tenant you add as the default storage region where objects that do not have assigned regions will be backed up.
- To add more tenants, repeat step 5 and click Add for each new tenant.
To remove any of the added tenants, click the delete icon next to the tenant.
- To change the default storage region to a different tenant, click Set as Default on that tenant.
- Once you add all the tenants you want to add, click Next.
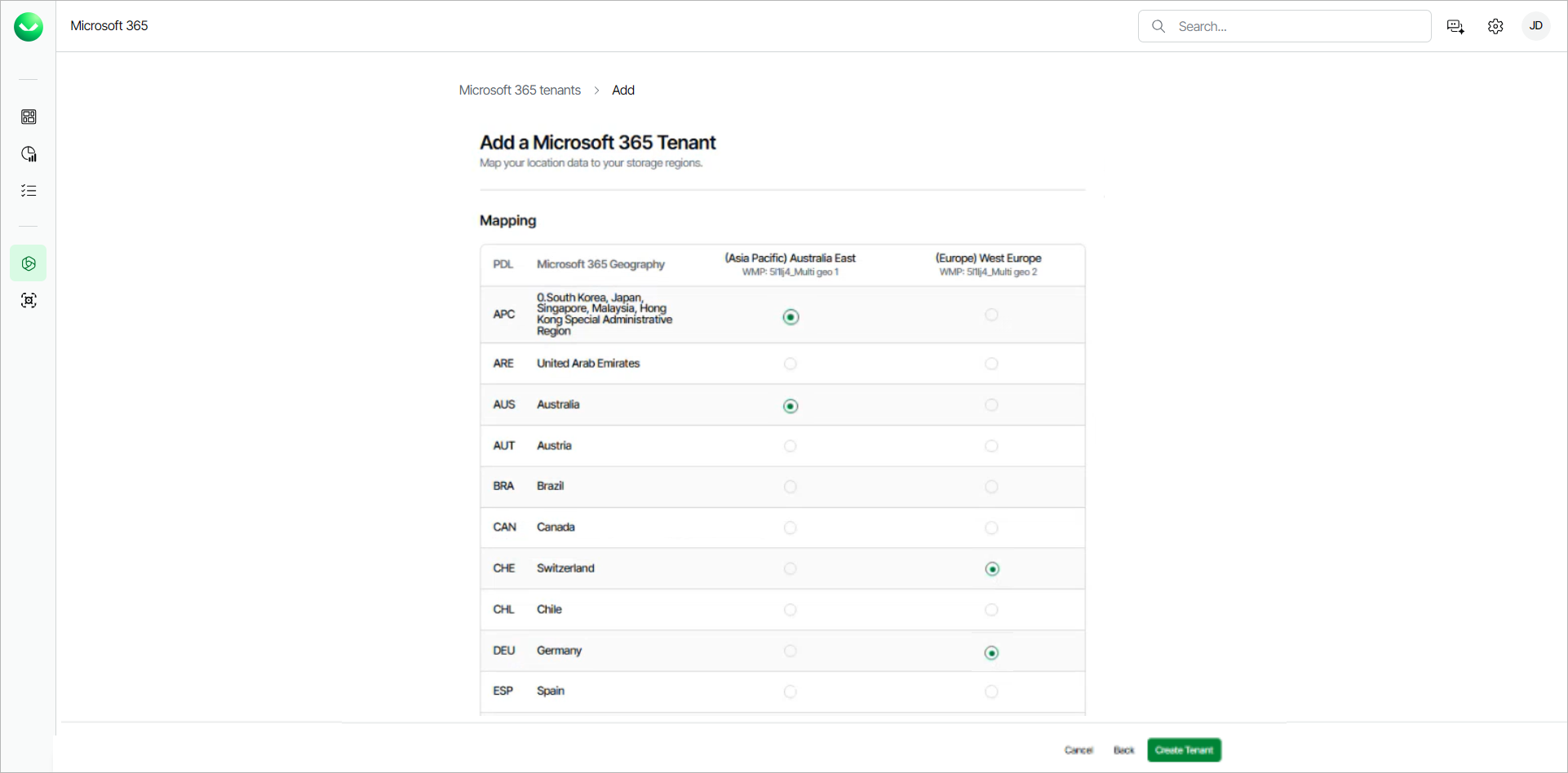
- In the Mapping section, map your location data to storage regions for each tenant. You can also change the default storage region from the Default Storage Region drop-down list.
- Click Create Tenant.
- Once the tenants are provisioned, you can create backup policies for each tenant and modify the region mapping.
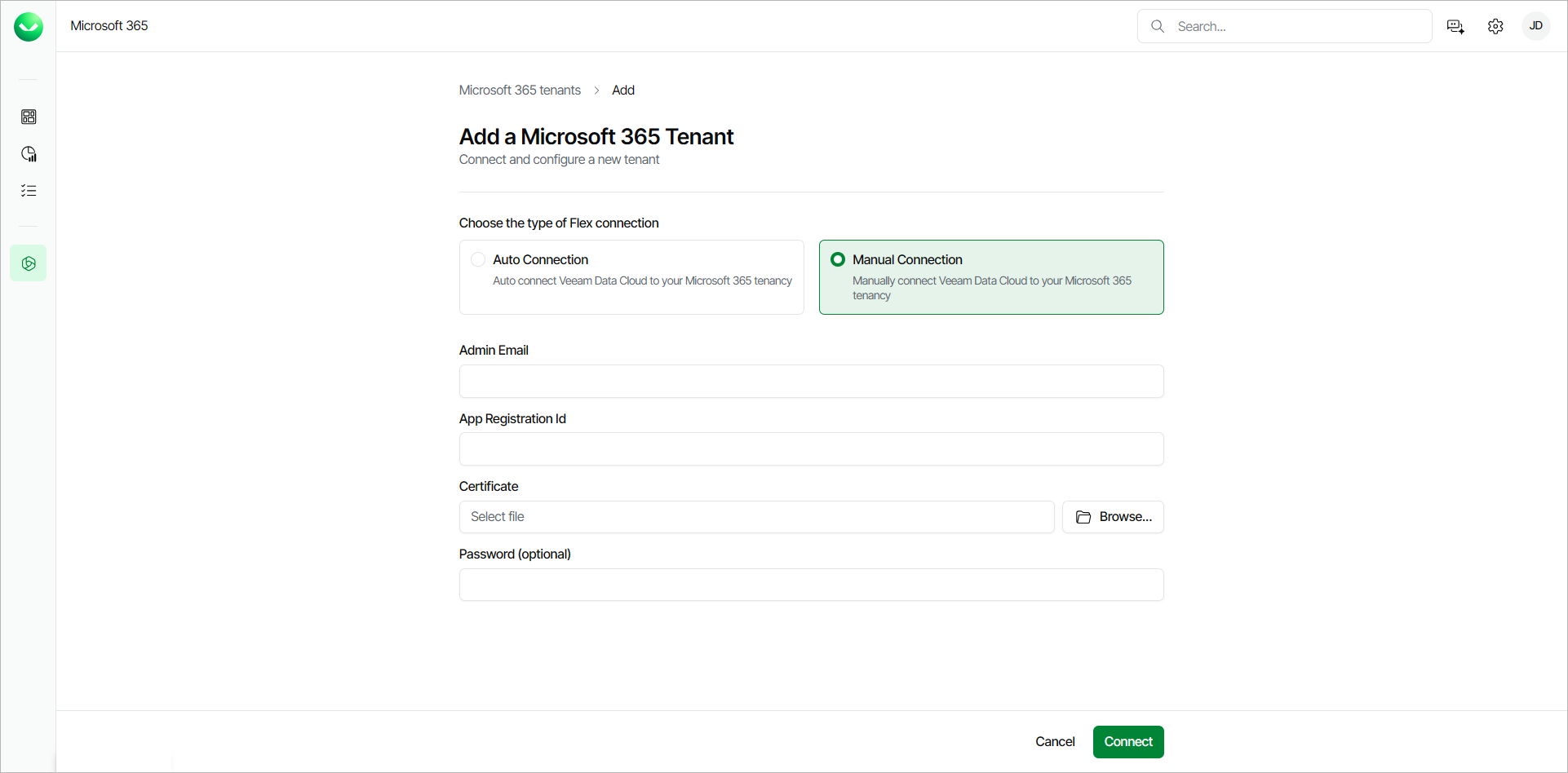
If you choose to manually connect Veeam Data Cloud to the multi-geo Microsoft 365 tenancy, do the following:
- In Microsoft Entra ID, do the following:
- Create a new App Registration.
- Assign the required permissions to the new application registration.
- Create and assign a certificate to the application.
X.509 compatible certificates from a trusted CA (Certificate Authority) and self-signed certificates are supported. For more information, see this Microsoft article.
- Export the certificate to a PFX file. You will use this file at step 4-c of this procedure.
- On the overview page of the application, copy the Application (client) ID value.
- In Veeam Data Cloud for Microsoft 365, in the Choose the type of Flex connection section, select Manual Connection.
- Specify the following:
- In the User Account Email field, type the email address of a Microsoft 365 user account that belongs to your multi-geo Microsoft 365 tenant.
- In the App Registration ID field, type the Application (client) ID value that you copied during the application registration in Microsoft Entra ID.
- In the App Certificate field, click Browse and select the PFX certificate file that you exported from Microsoft Entra ID.
- In the Certificate Password field, only type the password if you have exported the certificate with password protection enabled.
- Click Connect.
- Specify the multi-geo tenant settings:
- In the Tenant Name field, specify a name for the new tenant.
- From the Storage Region drop-down list, select a Microsoft Azure region where the backup infrastructure and storage will be provisioned.
For information on supported Microsoft Azure regions, see Backup Storage Regions.
- In the Retention Period section, set the number of Years or Days for the retention period of your backups, or select Unlimited to keep the backups for an indefinite time.
Once you set the retention period, you cannot reduce it. For more information, see Backup Retention.
- In the Select the service you want to protect section, make sure to select only the services that are available in the Microsoft 365 tenant that you are connecting to.
Veeam Data Cloud sets the first tenant you add as the default storage region where objects that do not have assigned regions will be backed up.
- To add more tenants, repeat step 5 and click Add for each new tenant.
- To change the default storage region to a different tenant, click Set as Default on that tenant.
- Once you add all the tenants you want to add, click Next.
- In the Mapping section, map your location data to storage regions for each tenant. You can also change the default storage region from the Default Storage Region drop-down list.
- Click Create Tenant.
- Once the tenants are provisioned, you can create backup policies for each tenant and modify the region mapping.
|
tip |
|
To ensure the manual connection is successful, confirm the following:
|