Using Existing Microsoft Entra Application
You can specify an existing Microsoft Entra application in your Microsoft Entra ID. Veeam Backup for Microsoft 365 will use this application for data exchange with your Microsoft 365 organizations during backup and restore sessions.
To use an existing application, do the following:
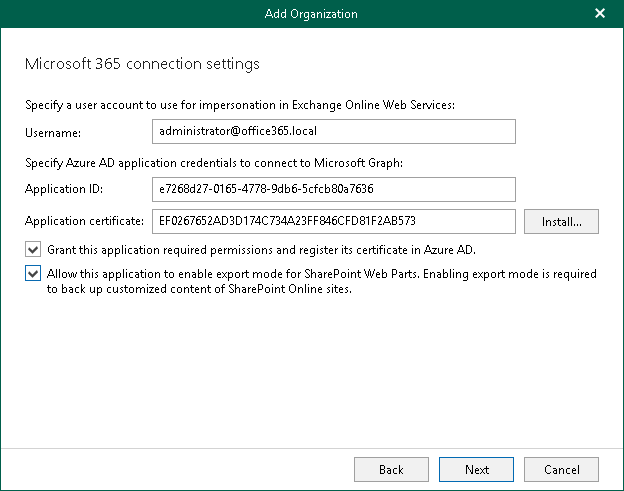
- In the Username field, enter a user account that you want to use for impersonation. For more information about impersonation, see this Microsoft article.
You can enter any account that belongs to your Microsoft 365 organization using the following format: name@<domain_name>.<domain>. For example, user@abc.com.
|
Note |
|
If you plan to back up public folder mailboxes, this user account must be granted the Owner role and have a valid Exchange Online license and an active mailbox within the Microsoft 365 organization. |
Keep in mind that if you select only SharePoint Online and OneDrive services to protect at the Select Organization Deployment Type step, Veeam Backup for Microsoft 365 displays the Specify organization name field instead. In this field, specify a domain name of your Microsoft 365 organization without the user name. For example, abc.com.
- In the Application ID field, specify an identification number of Microsoft Entra application that you want to use to access your Microsoft 365 organization.
You can find this number in the application settings of your Microsoft Entra ID. For more information, see this Microsoft article.
- Click Install to specify a TLS certificate that you want to use for data exchange between Veeam Backup for Microsoft 365 and the specified Microsoft Entra application.
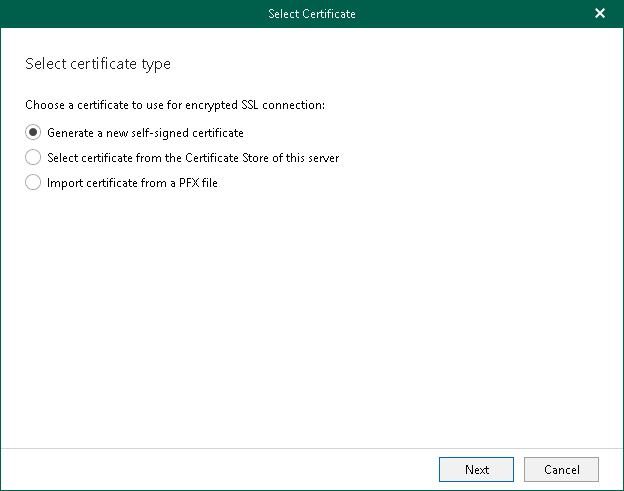
You can generate a new self-signed certificate or use an existing one. When generating a new self-signed certificate, Veeam Backup for Microsoft 365 will register it in Microsoft Entra ID automatically. Before using an existing certificate, make sure to register this certificate in Microsoft Entra ID. For more information, see this Microsoft article.
- In the Select Certificate wizard, proceed to any of the following options:
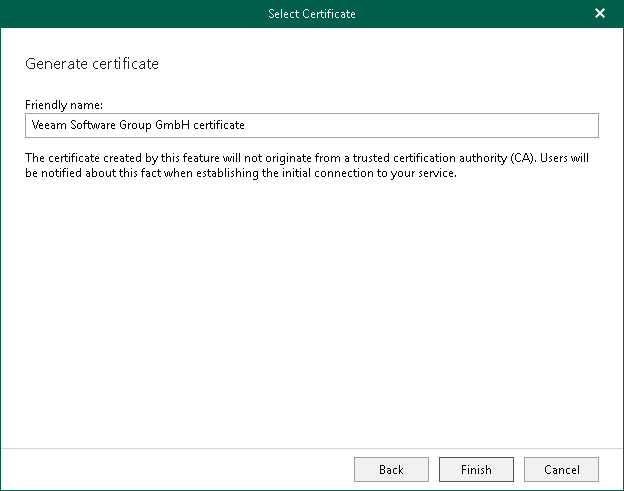
Generate a new self-signed certificate
|
Perform the following steps:
|
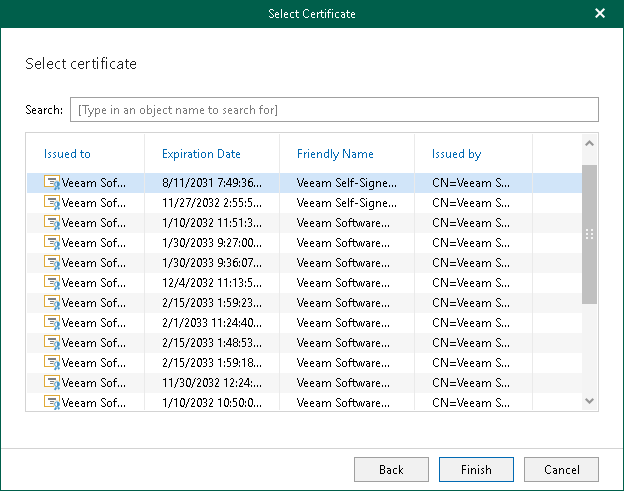
Import an existing TLS certificate from the certificate store
|
Perform the following steps:
|
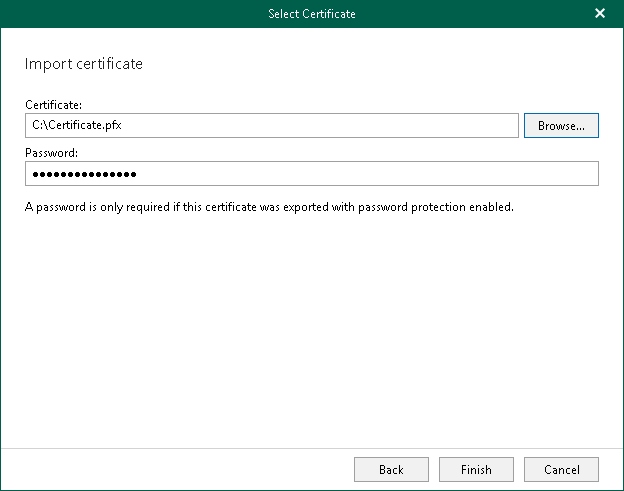
Import a TLS certificate from a file in the PFX format
|
Perform the following steps:
|
- Select the Grant the required permissions to this application and register its certificate in Microsoft Entra ID check box to automatically grant the required permissions to Microsoft Entra application.
Veeam Backup for Microsoft 365 will also register the specified certificate in your Microsoft Entra ID.
Keep in mind that you do not need to select this check box if you have granted the required permissions to the specified Microsoft Entra application beforehand and already registered its certificate in Microsoft Entra ID. If the Grant the required permissions to this application and register its certificate in Microsoft Entra ID check box is not selected, Veeam Backup for Microsoft 365 skips the Log in to Microsoft 365 step and proceeds to Finish Working With Wizard.