Step 5. Specify Instance Type and Enable Encryption
[This step applies only if you have selected the Restore to a new location, or with different settings option at the Restore Mode step of the wizard]
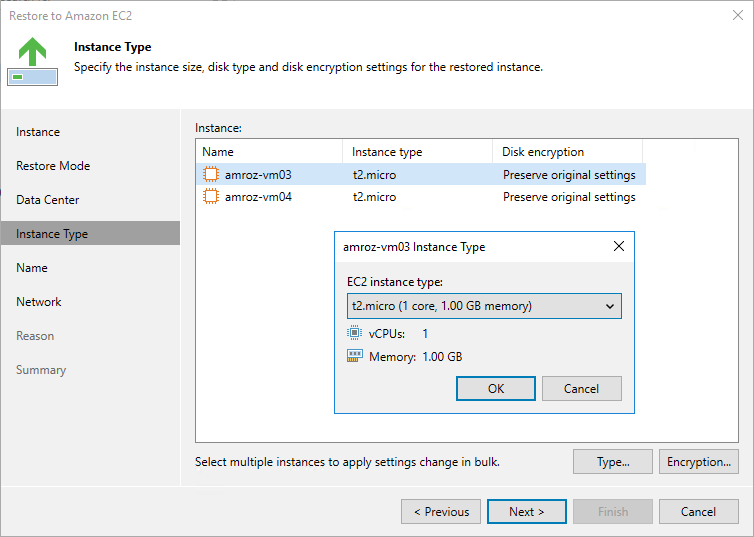
At the Instance Type step of the wizard, you can configure settings for the restored EC2 instance. To do that, select the instance and do the following:
- If you want to specify a new machine type for the restored EC2 instance, click Type and select the necessary type in the Instance Type window.
For the list of all existing EC2 instance types, see AWS Documentation.
- If you want to change the encryption settings of the restored EC2 instance, click Encryption and do the following in the Disk Encryption window:
- Select the Preserve the original encryption settings option if you do not want to encrypt the EBS volumes or want to apply the original encryption scheme of the source EC2 instance.
Note |
You will not be able to select the Preserve the original encryption settings option if the AWS KMS key that was used to encrypt EBS volumes of the source instance is not available in the region to which the EC2 instance will be restored. |
- Select the Use the following encryption key option if you want to encrypt the restored EBS volumes of the processed EC2 instance with an AWS KMS key. Then, choose the necessary KMS key from the list.
For a KMS key to be displayed in the list of available encryption keys, it must be stored in the AWS Region selected at step 4 of the wizard, and the IAM role specified for the restore operation must have permissions to access the key. For more information on KMS keys, see AWS Documentation.
Tip |
If the necessary KMS key is not displayed in the list, or if you want to use a KMS key from an AWS account other than the AWS account to which the specified IAM role belongs, you can specify the amazon resource number (ARN) of the key in the Use the following encryption key field. For Veeam Backup for AWS to be able to encrypt the restored EBS volumes using the provided KMS key, either the IAM role or user specified for the restore operation, or the IAM role used to create the restore point selected at step 2 of the wizard must have permissions to access the key. |