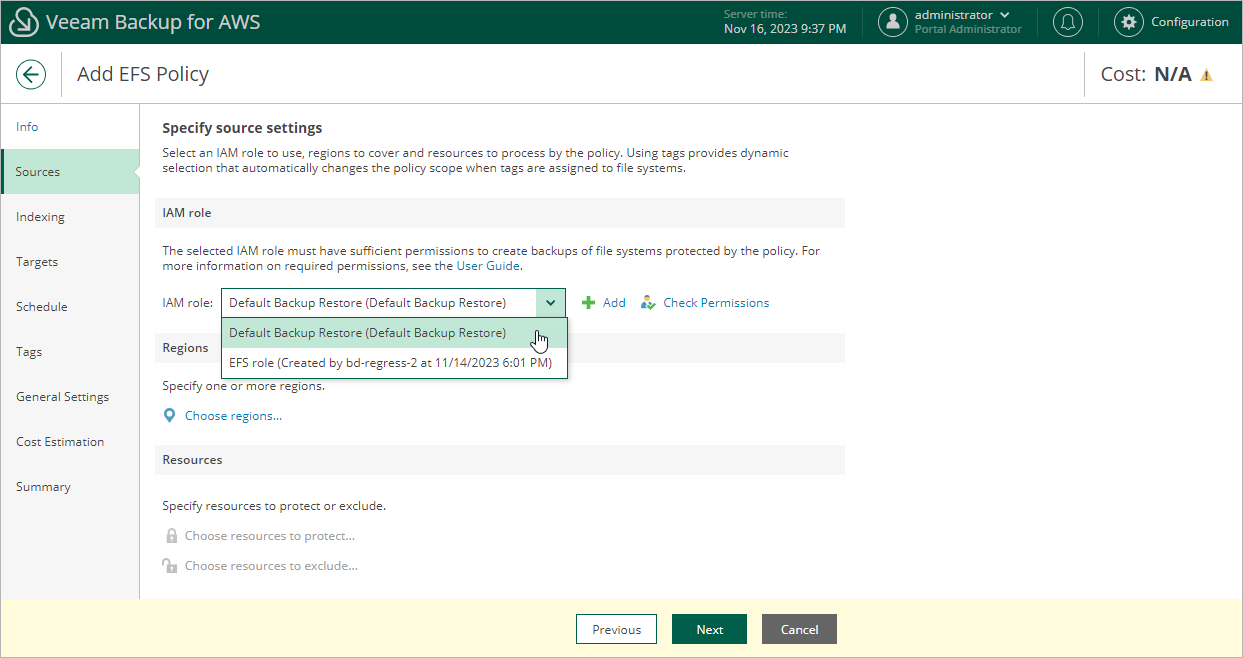
Step 3.1 Specify IAM Role
In the IAM role section of the Sources step of the wizard, specify an IAM role whose permissions will be used to access AWS services and resources, and to create backups of Amazon EFS file systems. The specified IAM role must belong to the AWS account in which the file systems that you want to protect reside, and mist be assigned permissions listed in section EFS Backup IAM Role Permissions.
For an IAM role to be displayed in the IAM role list, it must be added to Veeam Backup for AWS with the Amazon EFS Backup operation selected as described in section Adding IAM Roles. If you have not added the necessary IAM role to Veeam Backup for AWS beforehand, you can do it without closing the Add EFS Policy wizard. To do that, click Add and complete the Add IAM Role wizard.
Important |
It is recommended that you check whether the selected IAM role has all the permissions required to perform the operation. If some permissions of the IAM role are missing, the backup policy will fail to complete successfully. To run the IAM role permission check, click Check Permissions and follow the instructions provided in section Checking IAM Role Permissions. |
Related Topics