Managing List of Suspicious Files and Extensions
To keep the list of suspicious files and extensions up-to-date, select the Update malware definitions automatically check box. If the option is enabled, Veeam Backup & Replication will communicate with the Veeam Update Server (vbr.butler.veeam.com) daily and download the latest version of the SuspiciousFiles.xml file. The Veeam Data Analyzer Service checks the file for updates once a day at 12:00 AM.
Note |
If your backup server has limited internet access, you can update the list of suspicious files and extensions manually. For more information, see this Veeam KB article. |
Adding Custom Suspicious Files and Extensions
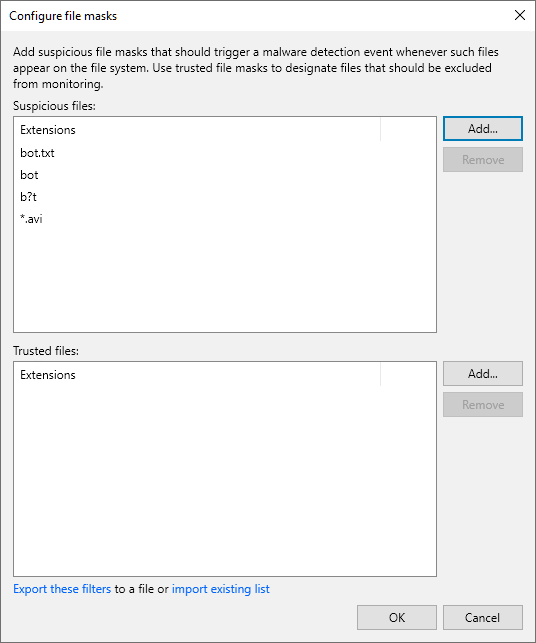
To add custom files and extensions that should be marked as suspicious, perform the following steps:
- From the main menu, select Malware Detection > General and click File masks to monitor.
- Click Add next to the Suspicious files field.
- Specify a file extension or a file name with or without extension. You can also use * and ? wildcard characters. For example:
bot.txt bot b?t *.avi |
Note |
Malware detection scan is case-insensitive. You do not need to add extensions or file names with different cases, for example, bot and Bot. |
- Click OK.
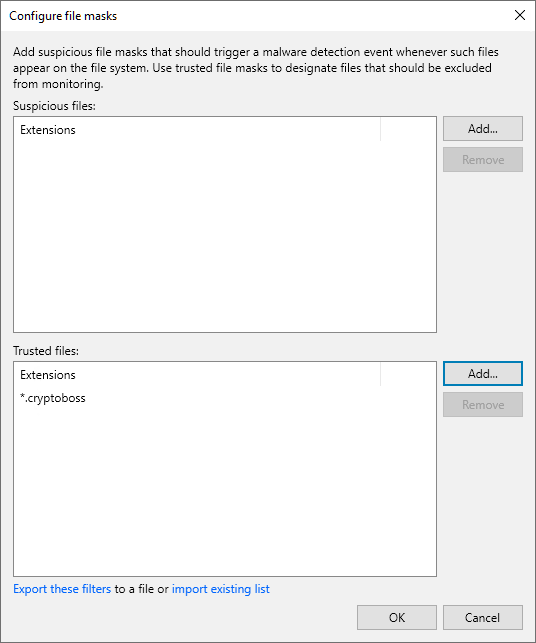
Excluding Suspicious Files and Extensions
To exclude a file name or file extension listed in the SuspiciousFiles.xml file and ignore it during the scan, do the following:
- From the main menu, select Malware Detection > General and click File masks to monitor.
- Click Add next to the Trusted files field.
- Specify a file name or file extension as it is listed in the SuspiciousFiles.xml file (the FileMask tag). For example:
*.cryptoboss |
- Click OK.
Note |
You can also add files and extensions to the trusted list from the Event Details window. For more information, see Viewing Malware Detection Events. |
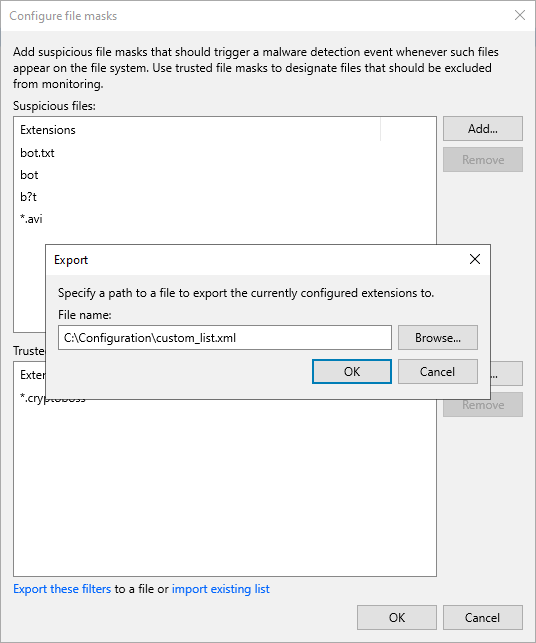
Exporting and Importing Custom Lists
You can export and import the list of custom files and extensions to/from a file in the XML format.
To export the list, do the following:
- From the main menu, select Malware Detection > General and click File masks to monitor.
- Click Export these filters.
- Click Browse and select the folder to save the list.
- Specify the name of the file and click Save.
- Click OK.
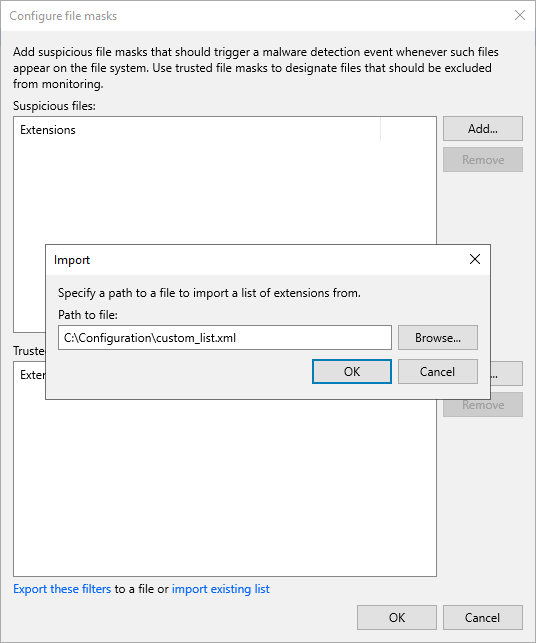
To import the list, do the following:
- From the main menu, select Malware Detection > General and click File masks to monitor.
- Click Import existing list.
Important |
The import operation will override files and extensions you specified earlier. It is recommended to export your current list before you import a new one. |
- Click Browse and select the folder where the file is located.
- Select the file and click Open.
- Click OK.
A valid XML Schema for the list must contain the following elements:
Element | Description |
|---|---|
RansomwareExclusions | Root element. |
Includes | Child element of the RansomwareExclusions element. Contains custom files and extensions that must be marked as suspicious. Can be empty. |
Excludes | Child element of the RansomwareExclusions element. Contains files and extensions listed in the SuspiciousFiles.xml file that must be ignored during the guest indexing data scan. Can be empty. |
Item | Child element of the Includes or Excludes element. Each Item contains a file extension or a file name with or without extension that must be marked as suspicious or ignored. Consider the following:
Note that files and extensions you want to exclude must be listed in the SuspiciousFiles.xml file. |
Example:
<RansomwareExclusions> <Includes> <Item>bot.txt</Item> <Item>*.avi</Item> <Item>bot1&2.txt</Item> </Includes> <Excludes> <Item>*.cryptoboss</Item> </Excludes> </RansomwareExclusions> |